Key Responsibilities & Actions:
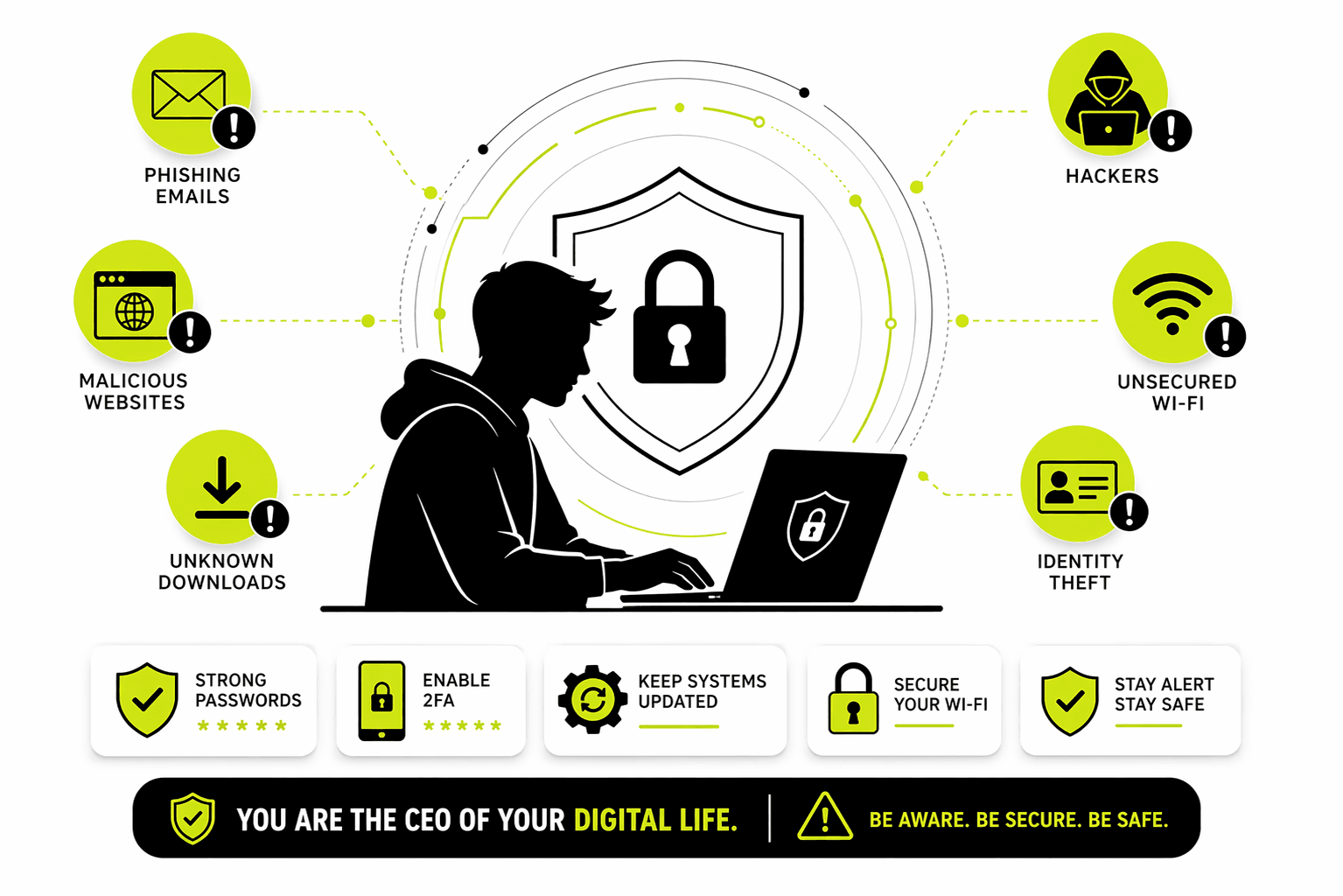
Threat Intelligence & IOC/IOA Management: I ingest and operationalize alerts from regulatory bodies (CERT-In, NCIIPC, FSISAC) and third-party subscriptions (RSA, VISA, Wipro). I translate raw IOCs (IPs, Hashes, Domains) into actionable blocks across Firewalls, EDR, Zscaler (Proxy), and IPS.
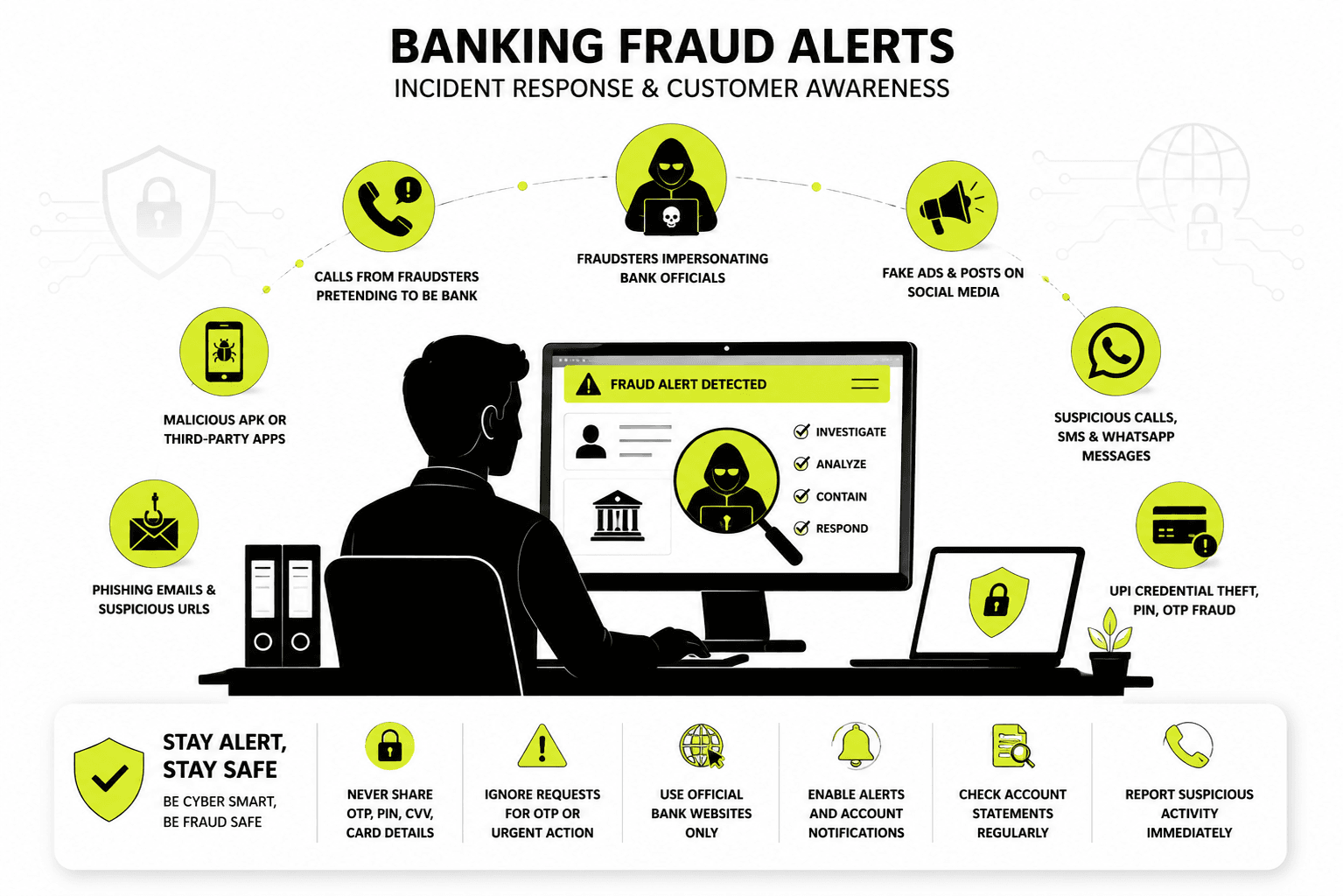
Brand Impersonation & Takedown (Cloud SEK, iZoologic): I hunt for and respond to digital brand abuse, including fake Facebook/Instagram profiles, phishing URLs, fraudulent mobile apps (APKs), and rogue websites. I coordinate with Marketing for validation and with Threat Intel partners for global takedown.
Data Leak Response (Scribd, GitHub, Dark Web): When PII, financial statements, or internal documents are exposed on public platforms (like Scribd) or code repositories (GitHub), I lead the containment effort, engage legal/GBO teams, and manage takedown requests to prevent financial fraud.
Credential Breach & Malware Stealer Response: I analyze stealer logs and combo lists from Telegram/Dark Web forums. I identify impacted users (employees & customers), force password resets, terminate active sessions, initiate AV scans, and coordinate with the CFMU (Fraud) team to check for unauthorized transactions.
Vulnerability & Botnet Management: I assess high-risk advisories (e.g., NetScaler ADC, FortiClient EMS) and botnet/malware infections on internal assets. I work with VAPT and system owners to validate exposure and remediate misconfigurations (e.g., exposed SSH ports).
Email & Phishing Defense: I analyze ESA anti-spam reports and phishing campaigns, extracting malicious URLs, hashes, and sender domains to block on Email Gateways and Web Proxies.
Cross-Functional Orchestration: I act as the bridge between the SOC (for historical footprinting), Network Team (Firewall blocks), Proxy Team (URL filtering), AV Team (Hash blocking), and Application Owners (password resets).
Impact:
Reduced threat actor dwell time by operationalizing intel within hours, prevented financial fraud by takedown of malicious APKs/phishing sites, and ensured regulatory compliance by responding to CERT-In/NCIIPC directives.