Cyber Threat Activity Linked to Geopolitical Conflicts
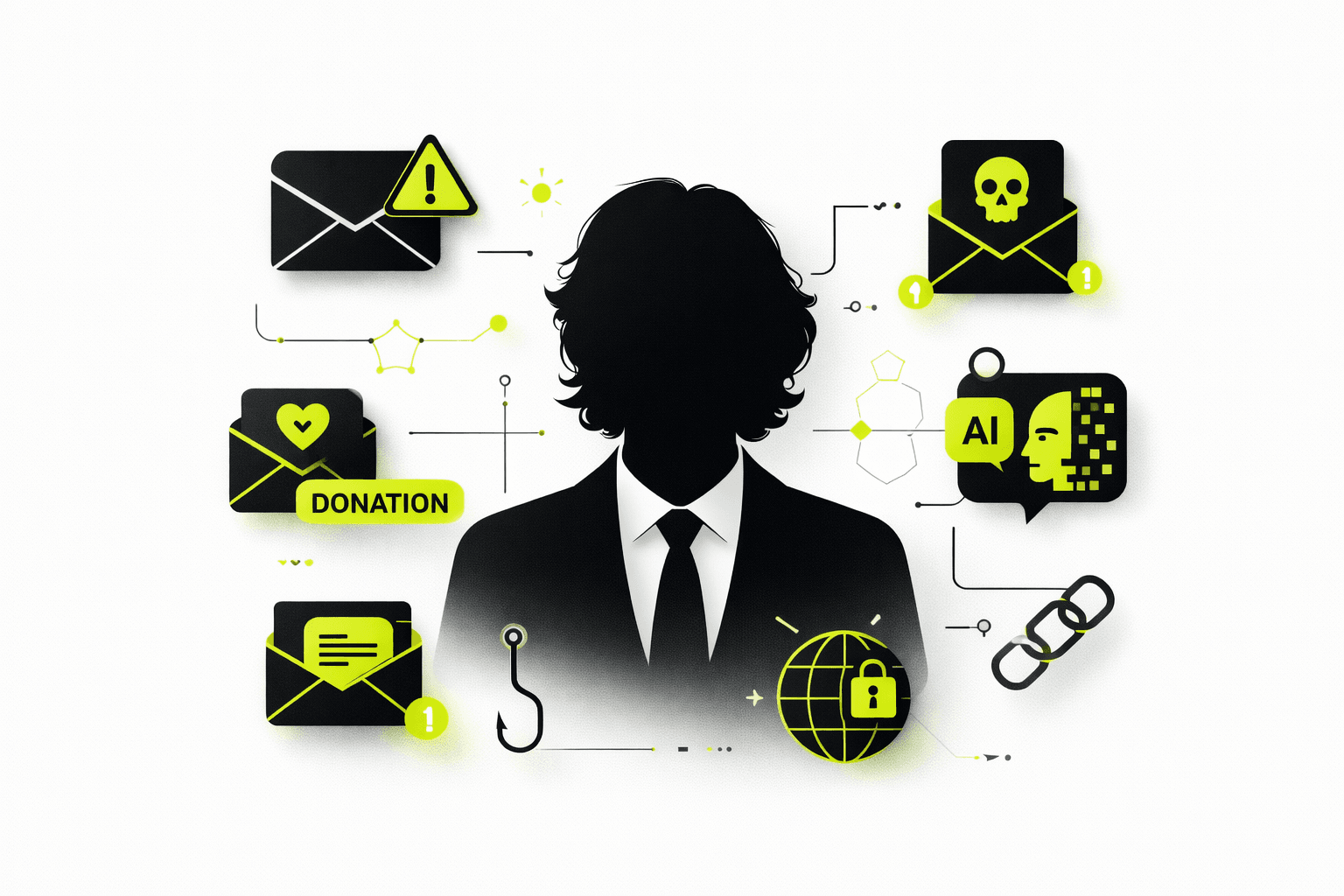
Geopolitical conflicts consistently correlate with an increase in cyber threat activity across sectors. Threat actors leverage uncertainty, high public engagement, and emotionally charged narratives to execute targeted campaigns. These campaigns are designed to manipulate user behavior, leading to credential compromise, malware execution, or the spread of misinformation.
Observed Threat Patterns
1. Conflict-Themed Phishing and Malware Campaigns
Recent activity indicates a rise in phishing campaigns using conflict-related themes as lures. Common delivery mechanisms include:
- Emails posing as “breaking news” or “leaked intelligence updates”
- Fraudulent donation or humanitarian assistance requests
- Urgent calls to action crafted to bypass user scrutiny
- Malicious links or attachments disguised as reports, images, or situational updates
These campaigns are engineered to exploit user curiosity and urgency, increasing the likelihood of interaction with malicious payloads.
2. Disinformation and AI-Driven Content Manipulation
Threat actors are increasingly using synthetic media to enhance credibility and impact. Key techniques include:
- AI-generated images, videos, and audio designed to appear legitimate
- Fabricated screenshots or falsified news content intended to provoke emotional responses
- Voice impersonation or message spoofing using AI to mimic trusted individuals
Such content is used to mislead users, influence decision-making, and facilitate secondary attack vectors such as phishing or social engineering.
Recommended Security Controls and User Practices
To mitigate risk exposure, the following controls and behaviors should be enforced:
- Do not interact with unsolicited links or attachments, especially those tied to current events
- Validate the authenticity of sources before engaging with or sharing information or report to SOC team for investigation, after found clean or safe email, then you can engage with email
- Avoid forwarding unverified content, including media and claims related to ongoing conflicts
- Report suspicious communications through official channels, including the cybercrime helpline (1930) or internal security teams
- Maintain strong security hygiene:
- Enforce Multi-Factor Authentication (MFA)
- Ensure systems and endpoints are regularly updated
- Apply caution when handling external files and communications
Operational Impact and Risk Context
Conflict-themed cyber campaigns are designed to exploit human factors rather than technical vulnerabilities alone. By leveraging emotional triggers and real-world events, attackers increase the probability of successful compromise.
From an organizational perspective, delayed reporting or user interaction with such content can lead to:
- Unauthorized access to systems
- Lateral movement within the network
- Data exfiltration or operational disruption
- Extended incident response timelines
Conclusion
This threat landscape reinforces the importance of user awareness as a critical layer of defense. Technical controls alone are insufficient without informed and cautious user behavior.
Maintaining vigilance, validating information sources, and adhering to established security practices are essential to reducing organizational risk.
Stay alert. Stay informed. Stay secure.
